The widespread adoption of blockchain know-how has created a number of safety dangers that may have an effect on customers and the popularity of recent tasks. Blockchain know-how has supplied a brand new strategy for conducting monetary transactions and data change. Nevertheless, the rising use of blockchain know-how and the monetary worth related to totally different blockchain and web3 tasks has created a number of safety issues. The Sybil assault in blockchain is likely one of the prime examples of safety dangers alongside flash mortgage assaults, phishing assaults, and rug pull scams.
It is very important study concerning the affect and various kinds of Sybil assaults to search out the most effective preventative measures. Allow us to study extra concerning the Sybil assault with examples and the trusted strategies for stopping such safety dangers.
Definition of Sybil Assaults
The easiest way to know Sybil assaults in blockchain would begin with their definition. Sybil assaults use a single node for working totally different energetic faux identities concurrently on a decentralized or peer-to-peer community. Such forms of assaults concentrate on undermining the authority in a good decentralized system by gaining management over a significant share of nodes within the community.
The faux identities assist in gaining a significant share of affect over a community. Profitable Sybil assaults contain risk actors who might perform unauthorized actions throughout the system. For instance, it might empower a single entity, equivalent to a node, to create and function a number of identities by means of IP-based accounts and consumer accounts.
The faux identities worsen the Sybil assaults impacts on blockchain by tricking the community and different customers into believing that they’re actual. The fascinating story behind the origin of the time period ‘Sybil assaults’ comes from a 1973 e-book generally known as Sybil. Within the e-book, one of many central characters, Sybil, suffers from dissociative identification dysfunction.
Construct your identification as a licensed blockchain skilled with 101 Blockchains’ Blockchain Certifications designed to offer enhanced profession prospects.
Forms of Sybil Assaults
Many of the guides on methods to stop Sybil assault in blockchain undermine one of the vital facets of the assaults. John R. Douceur defined the character of Sybil assaults and the 2 variants of Sybil assaults in his analysis paper. The 2 forms of Sybil assaults are the direct Sybil assault and oblique Sybil assault. Consciousness of the implications of those two forms of Sybil assaults will help find the best preventive measures for them.
Direct Sybil assault occurs when a malicious node interacts instantly with the sincere nodes throughout the protocol. Such forms of assaults are simpler because the genuine nodes can’t detect the faux nodes. On prime of it, attackers might manipulate real nodes to take actions that might align with the self-interests of attackers.
One other vital element you need to discover for Sybil assault prevention methods is the impact of oblique Sybil assaults. Oblique Sybil assaults happen when the faux nodes work together with one or a number of nodes related to the genuine nodes. As in comparison with a direct Sybil assault, hackers would make the most of middleman or proxy nodes for launching oblique assaults.
The middleman nodes in between the genuine nodes and Sybil node would function representatives of a single level of failure. Hackers might exploit the middleman nodes and launch an assault on sincere nodes. The issue with oblique Sybil assaults is that they can’t be detected as simply as direct Sybil assaults. As soon as a Sybil node influences the center nodes, it might result in breaches in genuine nodes.
Get conversant in the phrases associated to blockchain with Blockchain Fundamentals Flashcards.
What are the Causes of Sybil Assaults?
Sybil assaults have emerged as one of many vital safety threats which have affected many blockchain networks. One of many foremost facets of blockchain assaults and preventive measures is the identification of things that set off Sybil assaults. The primary reason for Sybil assaults is the vulnerability within the node creation course of. If the method for creating and working a node is simpler, then any hacker might arrange totally different Sybil nodes and implement the assault.
One other reason for Sybil assault in blockchain is the dearth of an efficient node validation system. With the proper validation system, you may simply detect and resolve the issue of Sybil assaults. Nevertheless, prospects for manipulation of the validation system might set off hackers to implement a Sybil assault.
The excessive quantity of monetary transactions on blockchain networks additionally serves as a set off for Sybil assaults. Due to this fact, blockchain protocols with a excessive quantity of monetary transactions are prone to be weak to Sybil assaults.
Begin studying Blockchain with World’s first Blockchain Talent Paths with high quality assets tailor-made by business consultants Now!
Affect of Sybil Assaults
Probably the most essential step in figuring out the best answer to Sybil assaults is detection. You have to find out about greatest practices for Sybil assault detection to keep away from their detrimental impact. You probably have just a few false identities on the blockchain community, then it could not current an issue. Nevertheless, a number of faux identities might have an enormous affect on the community. Right here is an outline of the alternative ways wherein Sybil assault can have a unfavorable affect.
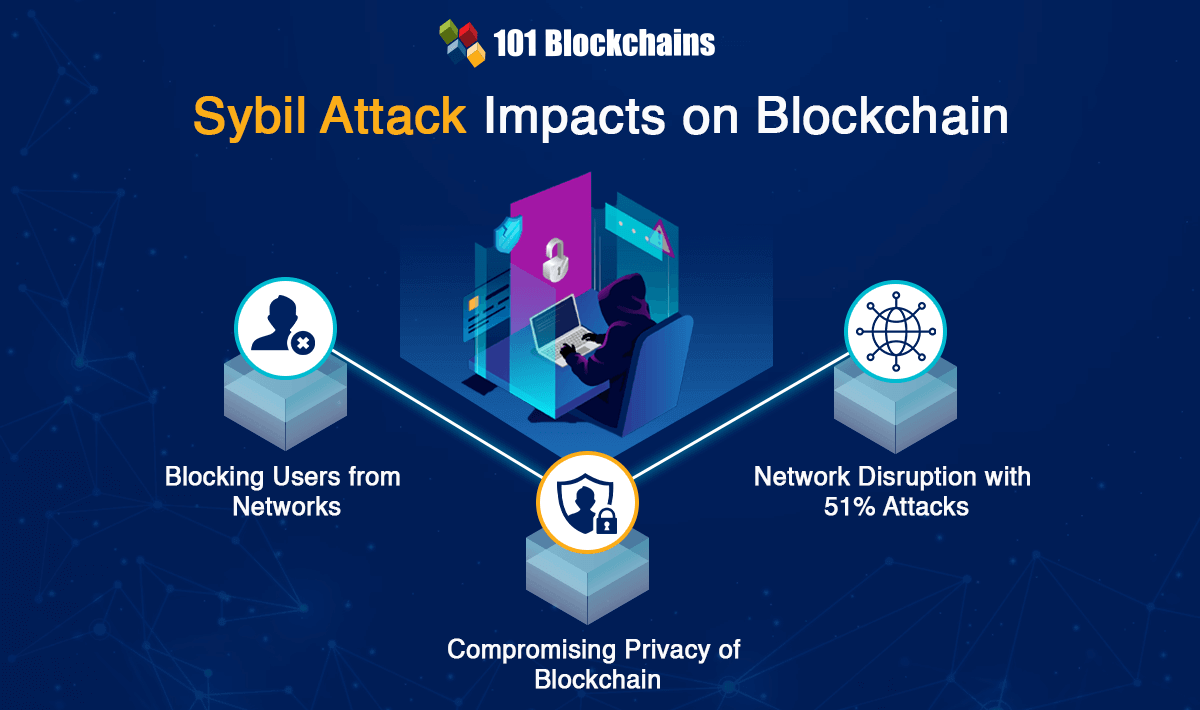
Blocking Customers from Networks
The foremost spotlight within the results of Sybil assault on blockchain networks is the restriction of customers from blockchain networks. Discussions on methods to stop Sybil assault in blockchain would draw consideration to the issues with creation of pretend identities. The faux nodes might overpower the genuine nodes in a blockchain community.
After Sybil nodes acquire management of the community, they may fully change the methods wherein the community operates. Most vital of all, Sybil nodes might refuse the transmission or addition of blocks inside a community. In consequence, the faux node might block different customers from accessing the community. The assaults might trigger a short lived drop in crypto values that may harm the popularity of blockchain protocols.
Compromising Privateness of Blockchain
Nodes are the integral parts in a blockchain community and handle the circulation of data within the community. Due to this fact, any sort of compromised node results in privateness dangers. The necessity for Sybil assault prevention methods emerges from issues concerning severity of privateness dangers for blockchain networks. Sybil nodes can extract details about different nodes within the community.
On prime of it, a Sybil assault might additionally result in compromised IP addresses of customers which will help in creating extra faux nodes. Privateness breaches are extra impactful for peer-to-peer networks. For instance, hackers might use Sybil nodes to spy on information transfers and monitor community visitors.
Community Disruption with 51% Assaults
The most typical objective of a Sybil assault is to implement a 51% assault on blockchain networks. One of many best methods for Sybil assault detection focuses on checking for a 51% assault. Such forms of assaults contain 51% of the community that includes false nodes. The faux Sybil nodes might overpower the votes of the opposite sincere nodes within the community.
Such forms of Sybil assaults could cause points concerning votes on main operational choices for the blockchain community. The 51% assault will help stop affirmation of transactions or ordering new transactions within the pursuits of hackers. Hackers might additionally implement transaction reversal for double-spending.
Begin your blockchain journey now with the Blockchains Fundamentals Course
Examples of Sybil Assaults
The affect of Sybil assaults reveals that they will trigger a whole lot of issues. Any blockchain community is prone to Sybil assaults. Should you find out about totally different blockchain assaults and preventive measures, one can find that the examples of a blockchain assault in the true world might present precious data. One of the vital distinguished examples of a Sybil assault is the assault on Verge cryptocurrency protocol in 2021. Hackers applied the Sybil assault to reorganize the blockchain community, wherein they deleted transactions of greater than 200 days.
Sybil assault has additionally been used to compromise the privateness of blockchain networks. Sure forms of cryptocurrencies, equivalent to Monero, concentrate on providing safe and personal strategies for finishing transactions. The Sybil assaults blockchain examples level to the assault on Monero in 2020, wherein a hacker disrupted the community and linked transactions to the IP addresses. Even when Monero managed to cease the assault, it couldn’t stop the leak of personal consumer data.
One other distinguished addition among the many earliest examples of Sybil assault is the Tor assault in 2014. The instance of the assault on Tor showcased the vulnerability of peer-to-peer networks to Sybil assaults. Attackers used the Sybil assault to find the identities and places of Tor customers. One of many vital highlights of the assault is that one hacker-controlled nearly 115 totally different relays from one IP tackle. In consequence, the hacker gained management over the community and accessed vital non-public data.
Tor additionally supplied one other instance of a Sybil assault in blockchain in 2020, as hackers compromised the community with a distinct motive. The attackers centered on Bitcoin homeowners who use Tor community. The hacker gained management over majority of pretend Tor relays and intercepted Bitcoin transactions by customers. Subsequently, the attacker used the knowledge to strip Bitcoin homeowners of their funds.
What’s the Very best Resolution for Stopping Sybil Assaults?
Greater blockchain networks equivalent to Bitcoin are tough to take advantage of with a Sybil assault. Nevertheless, you must know that Sybil assault prevention methods are appropriate for every type of blockchains. The affect of Sybil assaults might sound overwhelming and also you would possibly expertise issues in coping with the results, equivalent to lack of non-public data or crypto property. However, you may implement preventive measures to halt the assaults earlier than they happen. Listed below are the best measures for stopping the assaults.
Creating a Fame System
An important spotlight in Sybil blockchain assaults and preventive measures would level to the necessity for creating a popularity system. Sybil assaults depend on steady progress within the variety of faux identities. Due to this fact, a popularity system might assist totally different members have distinctive ranges of authority within the community.
Typically, members who’ve been part of the system for an extended interval have the aptitude to carry out extra interactions. Nevertheless, you could possibly not simply implement such forms of popularity techniques with out problems. It places duty on the person customers within the community.
The popularity mechanism can validate older members as sincere nodes and provides them the facility to override Sybil nodes. Fame mechanisms can discourage attackers as they’d transfer to a better goal with out losing time in creating new accounts and ready for energy over the community.
Identification Validation Mechanism
One of the vital noticeable penalties of Sybil assaults is the danger of dropping your privateness. You probably have an issue with privateness, then a popularity mechanism just isn’t the whole answer. The efficient route for Sybil assault detection would draw consideration in direction of validation of identification of recent nodes. You should utilize identification validation mechanisms for direct validation wherein a government would validate all the brand new nodes. Some techniques might depend on oblique validation the place verified nodes would vouch for the identification of recent nodes.
One other trusted addition amongst measures for stopping Sybil assaults factors at social belief graphs. Social belief graphs work by means of a complete evaluation of connectivity information between the nodes. Due to this fact, it may assist in figuring out and stopping irregular nodes earlier than they impose any harm.
The solutions for ‘methods to stop Sybil assault in blockchain’ information customers in direction of totally different methods for leveraging social belief graphs. For instance, some customers rely upon sparsity-based metrics, and different mechanisms contain evaluation of consumer attributes in a topological construction.
The graphs would then partition the a part of the community with Sybil nodes and forestall them from manipulating the sincere nodes. You will discover totally different instruments for utilizing social belief graphs, equivalent to SybilGuard, SybilRank, and SybilLimit. The very best purpose to make use of social belief graphs for stopping Sybil assaults is the flexibility to cut back the unfavorable affect of the assault.
Begin your journey to turning into an skilled in Web3 safety with the steering of business consultants with Web3 Safety Knowledgeable Profession Path
Conclusion
The Sybil assault is likely one of the most threatening safety dangers within the area of blockchain. As the specter of safety dangers jeopardizes blockchain adoption, you will need to concentrate on Sybil assault prevention methods. The most important drawback with Sybil assault is that it includes the creation of pretend nodes which seem as genuine nodes. It couldn’t solely have an effect on the privateness of customers but in addition result in large monetary losses for customers. Study extra about different safety dangers to blockchain and discover the best methods for resolving the problems.

*Disclaimer: The article shouldn’t be taken as, and isn’t meant to offer any funding recommendation. Claims made on this article don’t represent funding recommendation and shouldn’t be taken as such. 101 Blockchains shall not be answerable for any loss sustained by any one who depends on this text. Do your individual analysis!